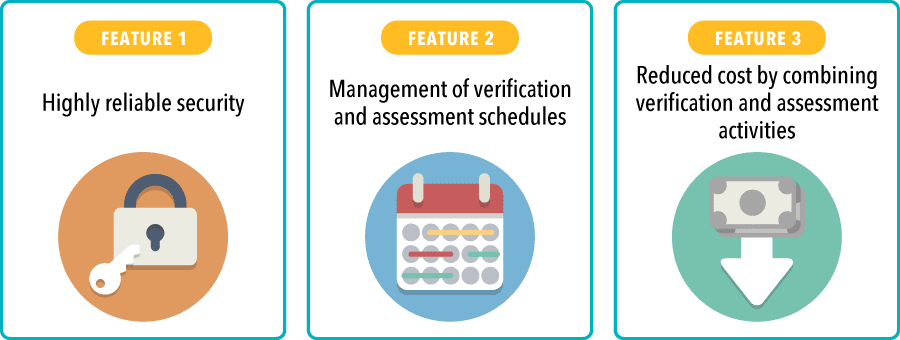
Features of Human Crest's Vulnerability Assessment
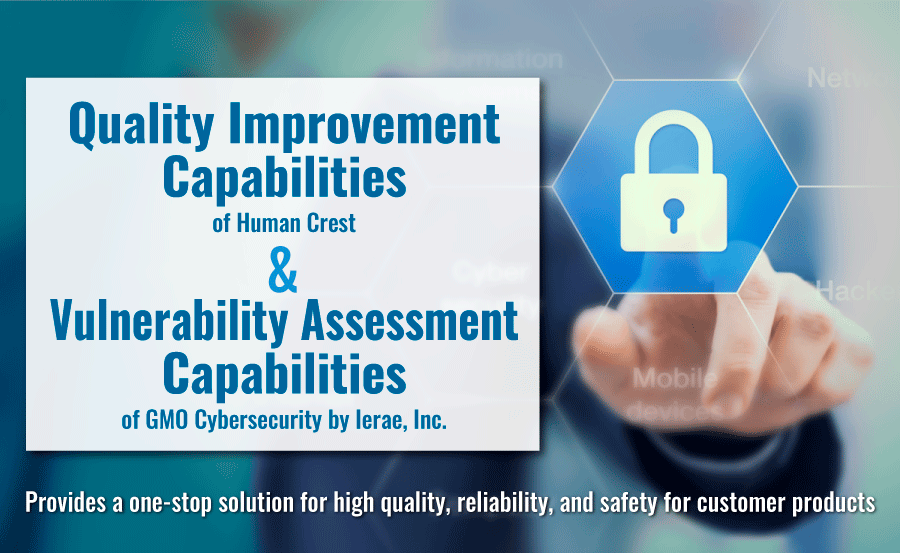
We have collaboration with GMO Cybersecurity by Ierae, Inc., a company specialized in vulnerability assessments using the world's leading analysis technology, to provide hybrid security assessment of Android apps, iOS apps, web apps, networks and IoT devices through both manual and tool-based approaches.
By integrating the handling of both product verification and vulnerability assessment, we can collectively manage information and achieving high quality and high levels of security at the same time.
Vulnerability Assessment Service Options
Process Flow to Assessment
Interview on details of the service or product to be diagnosed
We provide an estimate based on the details and documentation
Service application
After reviewing the estimate, the client applies for the service
Assessment conducted
Submission of the result report
Report presentation can also be provided as necessary
Submission of report on discovered vulnerabilities and results
Re-assessment
Re-assessments can be conducted as necessary
Service Examples
| Service Example ① | |
|---|---|
| Project | Pre-release testing and vulnerability assessment of an e-commerce website |
| Issues and requirements | Unauthorized access targeting a framework vulnerability was discovered. Use the opportunity of a complete e-commerce website overhaul to conduct both pre-release testing and a vulnerability assessment. |
| Approach | Implement work efficiently by scheduling the pre-release testing and vulnerability assessment together |
| Result | We were able to prevent incidents by discovering security vulnerabilities before the overhauled e-commerce website was launched. As the company has begun an organization-wide focus on security measures, we have been able to prevent security incidents since then. The company is also creating a set of Vulnerability Assessment Guidelines under supervision of Human Crest. |
| Service Example ② | |
|---|---|
| Project | Rental search engine for a major portal site |
| Issues and requirements | According to the company's internal rules, an assessment is required before every new release. The existing site is also periodically assessed once or twice a year. |
| Approach | Conduct a hybrid assessment of web apps using both manual and tool-based methods. Although no major problems have been identified to date, we advise on more secure methods whenever a minor issue is discovered. |
| Result | We were able to support the release of a highly secure and smoothly running website system. |
| Service Example ③ | |
|---|---|
| Project | Vulnerability assessment for the campaign website of an advertising and marketing company |
| Issues and requirements | A security incident occurred due to communication being insufficiently encrypted. |
| Approach | Respond immediately and conduct a security assessment |
| Result | Within a short period of time, we were able to provide a detailed report, making it possible to improve security. |
| Service Example ④ | |
|---|---|
| Project | Security assessments and quality verification of each service of a company that undertakes multiple projects |
| Issues and requirements | Conduct a pre-release verification and security assessment for multiple projects at once |
| Approach | Work efficiently by organizing schedules for multiple projects |
| Result | By handling the testing process and security assessment at the same time, we are able to achieve high levels of security and reliability, while improving quality and reducing costs. |
| Service Example ⑤ | |
|---|---|
| Project | IoT product verification and vulnerability assessment |
| Issues and requirements | Ensuring a safer and more secure system for the products, for which hacking prevention is essential as the number of users expands. |
| Approach | Verify and assess both the product itself and the web. Assess the equipment manually by dismantling it. Carry out verification and assessment in parallel, and repeat the process if any problem is found. |
| Result | By repeating the process of verification and assessment and executing all the work collectively, we are able to improve efficiency and reduce cost. |
 Quality Consulting & Quality Management
Quality Consulting & Quality Management Quality Assurance Team Building
Quality Assurance Team Building Quality Engineering & Software Testing
Quality Engineering & Software Testing Test Center
Test Center Test Automation Engineering
Test Automation Engineering Agile Testing
Agile Testing Security Assessment
Security Assessment Load Testing & Performance Testing
Load Testing & Performance Testing AWS Migration Testing
AWS Migration Testing Lynx — Automated Regression Testing Service
Lynx — Automated Regression Testing Service RakAPIt — API Testing Cloud Service
RakAPIt — API Testing Cloud Service Message
Message Profile
Profile History
History Company Structure
Company Structure Management Team
Management Team Contact Sales
Contact Sales